Extra security without extra work.
Scalability and security via intelligent automation.
- Automatically import configurations from security applications and deploy changes to thousands of devices within a few clicks
- Deliver unrivaled security based on network status with real-time monitoring and remote remediation
Devices. Applications. Networks. Complete security.
Take advantage of the Meraki platform and ecosystem partners to protect your workforce in the workplace.
Devices. Applications. Networks. Complete security.
Take advantage of the Meraki platform and ecosystem partners to protect your workforce in the workplace.
Resource Hub
Systems Manager
Systems Manager is the only endpoint management solution natively integrated with cloud networking devices.
Explore DetailsSecure 70k devices for the hybrid workforce
Simplify BYOD with scalable, enterprise-grade mobile device management.
Learn howContext-aware security
Exclusive integrations that provide a secure and seamless experience to the user, on and off network.
Watch videoSecure devices with SM at Black Hat Conference
Check out how Systems Manager was used with other Cisco security solutions at the premier cybersecurity conference.
Read blogSecurity that scales with your business.
Protect every endpoint with flexible device categorization, intelligent auto-deployment of configurations, and auto-mapping of identity to devices.
Get demo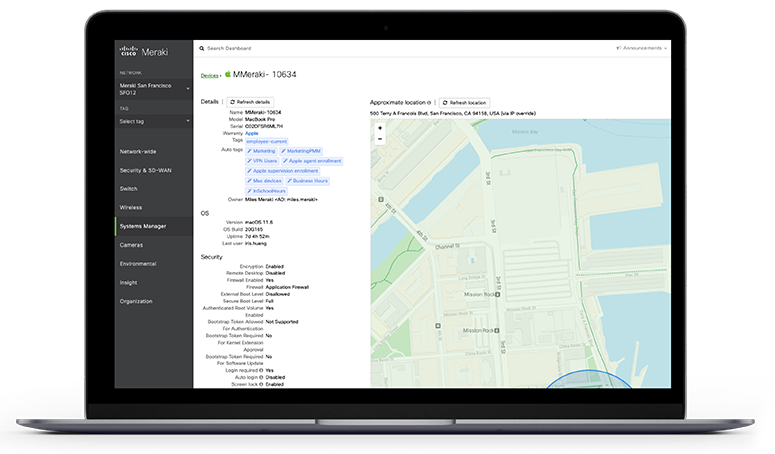

District saves 80% of admin time while managing 6,500 devices.
- Ease of deployment results in superior security and painless scale from 30 to 200 apps
- 5x productivity by leveraging APIs to automate repetitive tasks

400+ active users share their experiences, validated by TechValidate.
- 93% feel more confident about mobile security and adapting to hybrid work
- 45% saved over a quarter of the time required to deploy, maintain, or troubleshoot devices
Secure endpoints on the zero-trust journey.
Systems Manager is built to work seamlessly and dynamically with our cloud-managed Wi-Fi access points and cloud security solutions.