60% of Fortune 500 companies trust Meraki.
See how IT leaders optimize their networks, secure locations, and connect people, places, and things—by partnering with Meraki.
See all stories
93%
of current Meraki users are repeat customers.
16.5M+
active Meraki devices, plus more than 880 million connected devices on our network.
78%
of our customers recommend Meraki to other industry professionals.
Visionworks
Visionworks boosts customers’ and associates’ Wi-Fi experiences at 740 retail locations in 40 states—with Meraki access points.
Clarks
Clarks streamlines facilities management and reduces operating costs by using MT sensors and MV smart cameras.
“Cisco Meraki. It just works.”
Manuel Rangel, Network Engineer, Providence Health and Services
Qdoba Mexican Eats
Qdoba Mexican Eats utilizes a full-stack Meraki solution to save $300,000 annually in support costs.
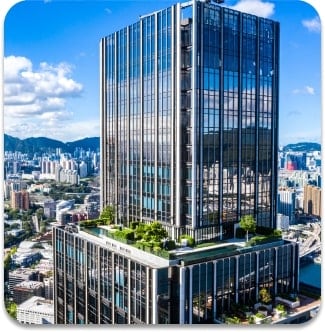
WPP
Cisco technology enables WPP to create smart campuses that encourage creativity and healthy ways of working.
Cisco helps Starbucks brew up efficiency through network automation.
A full-stack Meraki solution for premium customer experiences.
Browse our stories
Customers in the spotlight

College esports
How Meraki powers Ottawa’s multiple campuses and championship esports program.

A sustainable future
Learn how organizations leverage technology to cut energy costs and carbon emissions.

Pop-up Wi-Fi project
See how one savvy user created a portable Wi-Fi solution with Meraki products.
Smart banking spaces
Improved connectivity, intelligence, and security for financial institutions.